Turbulent times.
Turbulent times.
It appears that it was a coordinated action planned many days in advance. Without doubt also related to coronovirus.
We looked at the crypto index CMC200 and CMC200 without bitcoin which are volume weighted average price synthetic indices, now present in the mainstream with Nasdaq, Bloomberg, Reuters, Yahoo etc. Both indices culminated on 14 February 2020. In comparison, Nasdaq and S+P 500 CAC 40 DAX etc have all peaked on 19 Feb 2020.
There is a chance the the Internet will be completely transformed. One wind of change blows from blockchain tech community. Another from Communist China. Essentially all the technology we know, could disappear completely, and could be replaced by something completely different, a different set of protocols and systems.
For decades the so called “Internet” was some sort of virus which has infected the telecom industry and the whole economy, with the creation of electronic commerce. We have been brainwashed to believe in a dream. The dream that there could be some free independent medium of communication out there. Dream of more freedom of expression and more competition in business, benefiting consumers. However, there is no such thing such a free space. It is always going to be owned by someone, it is going to be prostituted to benefit the famous 0.1 %, the tech giants or/and similar centers of power. Or it will be owned by someone coming from China, like bitcoin already is, and as many businesses worldwide already are. The invisible hand of the market has a new very visible center of power.
In reality a free independent medium of communication has never yet existed. Let us stop being stupid and naive. In theory it could have been created, for example in the form of peer to peer software radio driven networking, but it simply has not been created yet (or not at scale). In reality we have been told lies. All this was rather or primarily just a game which many governments and national telecom monopolists and Internet businesses and even academics, have been playing for a long time. Game where some naive people work for free, for example be being open source developers, or producing free content for YouTube, or selling their technical capacity at a loss to other companies, more able to make use of it, or giving away for free their research expertise, etc. Or opening all sorts of businesses sectors to unfair competition.
Naive actors work more or less for free, while other become super rich. The telecom markets and the media markets worldwide have been transformed. National telecom companies have been disrupted by fierce international competition. Jobs have been moving to countries which have been able to profit from this situation. Long time ago, it was Finland. This time is over. Competition has destroyed many industries and millions of jobs have been displaced.
Then came new monopolistic vertically integrated omni-scient Internet and media and electronics giants, which are now looking at AI as the logical next step. Now is China making Internet telecoms and 5G their exclusive playground with a new Internet standard proposal. All these things are children of naive and stupid telecom deregulation, based on the illusion that telecom services can be free, that they have no price tag. This is an illusion which appears if you are short-sighted and you consider the cost of was needed yesterday, with the technical means of tomorrow. France, United States, UK Germany alike, have abandoned and neglected their telecom industry, but it did’t go South and bankrupt. It went East and become one of the most profitable sectors of the economy. Finland was just one stop on the way. Glorious country Finland, an example to imitate, but at the end we lost it, or lost it for Europe.
Here is one very timid way how a new and major game change could happen and disrupt the Internet. It is unstoppable decentralized Internet underpinned and disrupted by Ethereum. Or it is the DFINITY unstoppable tampeproof serverless platform. The main idea is that with this sort of system, to take down one service or a web site, an attacker needs to attack the whole network. We are talking about radical decentralized censorship-resistant changes in technology and critical infrastructure, where autonomous apps collaborative systems are running without an apparent owner.
Such systems can have far reaching consequences for business. For example Ethereum network will be important, but the price of optical fiber networks or other telecommunication services will go down. This could in fact become a tipping point, where the status quo could be changed for many other things, like how electronic commerce works, for example. It could make things such as TLS and packet switched networks and credit cards and even banks totally obsolete.
At this moment Google can blacklist this Chrome extension and kill this innovation. There will certainly be ways to block DFNITY systems too.
This sort of blacklisting of apps and technical standards, is how Google runs the world. Google has done this before in all impunity, you go from from “hero to zero” overnight. Or was it an accident? Not only web sites are subject to hostile take-downs. Businesses also. Recently CCN was in the dark, a major crypto currency news outlet, because Google searches stopped showing them. Interestingly, during this period CCN have received several offers to buy and take over their company… Another example: Twitter bans Ripple CEO Schwartz. Few more examples are the troubles of Zynga, Salesforce, Tinder, cited at DFNITY FAQ page.
We come here what is certainly the worst ACHILLES FEET of most crypto currency businesses. Blacklisting threat. First some sort of creepy suspicion of money laundering, so badly treated or blacklisted by certain banks. Then maybe facilitating sex or drugs-related criminal activity on the Internet. Finally, I forgot, Vitalik is Russian and he met with Putin. So these innovators can and will be blacklisted at any moment. The same type of blacklisting is also applied to Chinese telecom business.
We see a pattern, how incumbents can control censor and bend the innovation, in order to benefit them, with help of naive governments and legislators and regulators. Also with help of largely corrupted mass media, which companies such as Google largely control, well indirectly, through incredibly large advertising budgets.
Possibly Google and other incumbent players will develop some sort sort of clone, or imitation of this technology. In general, you can expect very nice things from Google technology-wise and security-wise. They are not a new Microsoft, they have always done extremely well in my opinion, in particular on security, and gave been a good example for others, not a bad example. However, they are likely to be nasty with just any independent anarchist crypto startups. This is life. Though Google do understand technology, they are likely to distort the reality to fit their narrow-minded business agenda. They are likely to commit serious mistakes motivated by narrow short term business interests.
Recall that France has invented the electronic commerce, literally everything, like buying your train ticket on MiniTel, or enrolling at a university, or sex chat business. But they FORGOT to develop one important invention, the one of email or maybe text messages. Text messages came from Finland, and email was invented by some silly underpaid academics, who did not like paying for their communications, blissfully ignoring the fact that their universities and government have paid a lot for some networked systems to exist. Why the French did not invent text messaging or it remained marginal? Maybe because it would make their national monopolist telecom champion business lose billions (made from local phone calls, to an answering machine for example). Most telecom CEOs have missed exactly this: like for about a decade they have underestimated by a factor of at least 10x, the amount of income they would themselves make from silly “text messaging”. In business we call this cognitive limitation for the managers (a certain inability of incumbents to understand their own business sector).
Likewise, Google is likely to miss the train here. For sure Google can and will work to influence how Internet and electronic commerce is done, protocols, standards, business etc. But they will miss in many ways in which and how disruptive, more decentralized blockchain-based and crypto-rich and Internet could be. They will fail to grasp the possibilities offered by a new crypto financial industry where money is NO LONGER stored at banks or exchanges but it is stored at electronic wallets.
The incumbents will just look at fewer things which will benefit them. Likewise they do not get it about telecoms and 5G. So many things which are not their business. Google is likely to fall below expectations. Elsewhere, opportunities increase faster. They could actually literally explode, see how Bitcoin got out of leash and out of control since 2009, and could became equal to Google on market cap question tomorrow say in 2021. Likewise 5G is coming massively and Google also thinks, we simply do not care. They think: we do our job and dominate electronic commerce anyway, whatever it is. However they do not get the following thing: incumbents almost always fail or weaken (see Microsoft) when the technology changes. And so really Google does not want any big change, probably. And they are wrong.
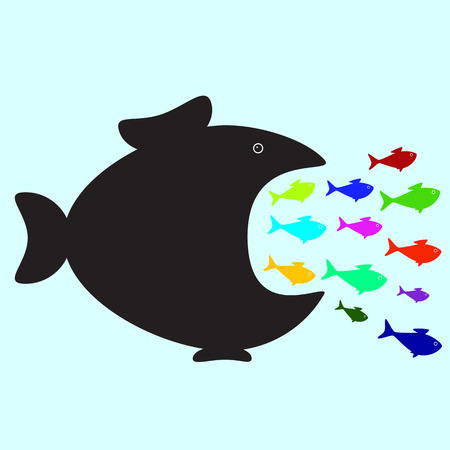
For Google Ethereum or DFNITY are small fish. They will first fail to disrupt Internet not only because because Google Facebook and Amazon can afford to ignore them. Also because Google Facebook and Amazon actually ignore a bigger picture. Their mortal sin is that they are not at all trying to disrupt the Internet, because they are happy to be large monopolistic businesses.
If so there is only one real disruptor left. Remember that China have their own crypto currency projects. Be scared of Chinese clones of the players in our game such as NEO or TRON, where David (Ethereum) is playing his naive stunt against Goliath (Google). These are not just about hiding money of rich Chinese who would like to live in Europe or the US or facilitating private cross-border transactions. We have a crypto belt and road, and we have a digital silk road. These are the real forces which seem unstoppable today. The new Internet protocol proposed by China Huawei has more tracking, is more centralized and allows more censorship. Ethereum is a joke compared to telecom and Internet giants and their games. We are completely unprepared, and people in China are a lot smarter than people in the hypocritical divided West, petrified by the unfolding of a new financial and public health crisis and by an acute depression.
Going back to the dream. We have been brainwashed for decades to believe that Internet is permission free, and tried to build crypto currency to be permission free (and decentralized and democratic). In reality all these are just power games where big business monopolist empires emerge, and most people lose, investors, entrepreneurs or employees alike. Now we are made to believe that Internet is going to become even more decentralized with Ethereum or DFNITY and it is a great thing. It is stupid dream and it is simply not happening. In reality it will become more centralized and even more monopolistic, and yet more centered around an authoritarian China, the ultimate winner of decades old worldwide telecom industry consolidation. Today when the whole planet has its eyes at one short term virus, but have been ignoring another virus, the virus of stupidity and naivety, typical in the West from 1968 and today’s millennials, with their super naive ideas about life. Conspiracy theories also come form here, they are the other side of a coin, the coin of not trying to understand the world in which we live, and being very naive about it, which makes young people prone to manipulation one way or another.
We regret the inability of our power centers to truly embrace new technology in a positive way. Except when pursuing very narrow and almost always toxic business interests. We regret our stupid delusions which come from the fact that we believe too much our own propaganda, about freedom and better life. Christianity promised better life tomorrow. Internet promised better life today, but it is not real, it is like a computer game. On this planet business with AI and authoritarian empires are working hard to enslave people and control our lives and resources of this planet. Good things do not come for free. Nations who are not trying to be strong players in the technology space, are being colonized by other (smarter) nations.
Technology and coronavirus are the real unstoppable forces: they are both “viral”. One however is a slow exponential, the other a super fast exponential like coronavirus infections worldwide. Always fight the fast exponential, and embrace the slow exponential. Both are very strong if not unstoppable, but the second can be our friend tomorrow.
If we want to survive, we need to stop being naive about science and technology: they can disrupt and transform, but not everything which shines is gold. All of telcos Internet bitcoin Ethereum governments and also academics have lied to us a lot every day about the new technology. I guess life will always be like this: the more money and power is at stake, the more naive young people get badly informed, if not brainwashed. Free content and free services and free press and free software and free game are like cancer. They are meant to enslave people, to own them, and they are a junk-grade imitation of a civilized society, where everything is free, but you are an underclass slave, and ‘sponsors’ or ‘owners’ of all this world consider that they own you, and you are expected to work for free also. If you’re not paying, you’re not a customer, you’re the product being sold, and you have little or no legal rights whatsoever, and simply just a victim of a well organised game, where humans are an object of intense manipulation, in many ways including through addiction, leading to a totalitarian economy with mass surveillance and AI at the very center.
Private money has arrived. Crypto winter is over. At least for India.
The supreme court of India has overthrown their 2018 ban on crypto currency.
Today, Jo Grady, general secretary of my university trade Union (UCU) wrote these words to all academic staff who are members of the union:
“we are asking you to withdraw, where possible,
from activities relating to the REF […] […]
These activities are important to employers but they damage our sector.
They rely on inappropriate metrics of quality; that create
perverse incentives and prevent us from doing the front line
teaching, research and professional services work that really matters.
Exercises like the REF tend to increase our workloads,
waste money that could be invested in staff, and exacerbate
our anxiety and insecurity by subjecting us to unfair,
unhelpful performance management procedures. “
No comments.
Exactly 30 years ago, Stasi was dissolved. 13 January 1990. 91,000 full time employees and 189,000 unofficial collaborators and informants lost their jobs and privileges.

The German government has done a lot to preserve anything which Stasi has ever done. Some links:
Remark added later: 13 January 2020 was the first case of Coronavirus outside of China. An old lady from Wuhan… Conspiracy theories will thrive!
A new documentary tells the story of the discovery of one of the most important cryptography papers of all times. We are talking about an extensive technical report written in German language and entitled “Kurzgefasste Darstellung der Auflösungsmethoden”. For some 80 years it has remained classified, part of the so called Gustave Bertrand WW2 archives.
It was written presumably in France, in early second half of 1940, by Marian Rejewski and Henryk Zygalski, though the author names are in fact, not at all specified(!). It seems also that Alan Turing, Dilly Knox and other UK authors were also involved in producing this report. This is, because, instead of a list of authors, this report is written as a summary, or a survey, and very much like a manual, summarizing what was known to the whole group of people. It contains in fact a very clearly marked list of named contributions, many of which are made by UK cryptologists. For example all Jeffreys, Herivel and Knox are named inside as contributors, see Fig. 1 here. If the authors are not specified, and in absence of further factual discoveries, this report could also be considered as joint work contributed, directly or indirectly, by all people named inside(!).
It is a concise and very detailed summary of all known attacks on Enigma as of 1940. A monumental document which shows how cryptography and cryptanalysis have developed in 1930-1940, with a summary of presumably everything which was known to the allies [Poland,France and Britain] about breaking Enigma codes, at the time.
In fact not quite so or not yet. The title “Kurzgefasste…” suggests that a longer even more detailed document may have existed, which question is also discussed inside this documentary. In fact we know for sure, that some additional cryptographic and signals intelligence knowledge and expertise, and numerous additional concrete decrypts of WW2 messages, have existed at the time, and were known only to yet fewer people. It is believed that these things were however shared with Bletchley park, or/and countries more directly concerned such as Switzerland, more on the need-to-know more ad-hoc basis. It was estimated [as reported by Jean Medrala who has spent a lot of time studying French military archives] that about 50% of decrypts done by Polish code breakers working on the French soil were dissimulated, and not communicated to Bertrand, for some time, and at least until the late 1970s, when Bertrand has written his memoirs. In particular we should consider that knowledge and expertise concerning the decryption of Russian messages was considered as even more sensitive than anything concerning Enigma. It was known to a yet smaller circle of people and almost certainly this part was also not known at Bletchley Park either, and was shared with the UK on a different basis. Private correspondence of WW2 code breakers, preserved by their surviving family members, suggests that they did not in general trust Bertrand, who officially worked for the Vichy government(!). We expect that additional facts will brought to light, and will be published in the near future.
Observation: We should note that the method of Sillies, described by Welchman in The Hut Six Story, will be the first one, not known or not shared with the Polish and French side. This even though very clearly the report shows how the attack method of Herivel, from exactly the same period became operational, with contributions made on both sides of the Channel. These methods were operational in second half of 1940, after France was overrun, and was based very clearly on observations and data gathered in Bletchley Park for a longer (earlier) period, but maybe not shared anymore or not in full. This is a significant observation, and this is maybe how the report can be dated to be closer to June than September 1940. Or this is how the XYZ or Polish-French-English cooperation has slowly ended, and a new era of code breaking run and dominated by Britain alone has started.
Here is the documentary to watch:

On a picture: an original French-Polish made Enigma machine with ABCD keyboard from the collection of Pilsudski Institute in London. Only 2 such machines exist.
P.S. This report could be cited as follows:
Marian Rejewski, Henryk Zygalski and other undisclosed authors:
Kurzgefasste Darstellung der Auflösungsmethoden. Bertrand archives, Service Historique de la Défense, Vincennes, France, DE 2016 ZB 25/6, Dossiers Nos. 281 and 282, ca. 1940.
Added in 2020:
In 2004 I have published a paper [Crypto 2004, Santa Barbara] in which I explain the concept of the so called Bi-Linear attack on DES. The old attack was not extremely strong. It is possible to see that two conditions would be necessary for such an attack to somewhat work well in cryptanalysis of DES:
Z*(a+d)=0
Needless to say they don’t, and this attack is just unthinkable (a detailed description of one attack of this type can be found in section 11.2 of this paper). There are extremely few cases where point 1. would work and in fact the situation is far worse for point 2.. It is possible to see that the probability that Z*(a+d)=0 for a random Boolean function is
(2^-9.5)^2.
3. Moreover it is easy to show mathematically that such a Boolean function cannot be non-linear and balanced at the same time [a little theorem which we leave as an exercise for a reader, solution will be published soon].
So we have an extremely weak attack on DES which does not and cannot work due to points 1. 2. and 3. However:
The idea is that we need to relax this attack a little bit and eventually the obstacles 1. 2. 3. can be removed or circumvented.
It will come as a shock to anyone who has ever studied DES but linear annihilators DO EXIST in few cases for the original DES S-boxes. In fact we have these two examples:
(1+R14+R16)*(W4+X4+Y4+Z4+1+R12+R14) = 0
(1+R16+R17+R20)*(W5+X5+Y5+Z5+1+R17) = 0
Specialists of Boolean functions would say that “some output linear combinations of DES S-boxes are 1-weakly-normal” see this paper. Or that “some linear combination of output Boolean components is linear on an affine space of dimension 1 (a coset of a certain linear space)”.
This is actually a very strong property. Extremely few Boolean functions have this property (actually also about 2^-9.5 of all Boolean functions on 6 variables).
So obstacles 2. and 3. are removed. Where do we get from there?
The question really is how to remove obstacle 1. as we are NOT allowed to change the wiring of DES in order to make the job easier for us. The answer is that we need an attack able to exploit properties such as above. The existence of such an attack has been an open problem since 1985, the famous mystery paper by Adi Shamir. This attack is no here, is now public.
For now, let us look at the underlying DES facts.
Why is our property related to the one observed by Shamir? Shamir observes that for many DES S-boxes the sum of 4 outputs such as (W1+X1+Y1+Z1) for the 1-st S-box is strongly biased (in fact only when input b is fixed). If so either (W1+X1+Y1+Z1+R01) or (1+W1+X1+Y1+Z1+R01) would have a large number of annihilators (it is easy to see that the number of annihilators depends on the Hamming weight or the number of 1’s in the truth table of a Boolean function and nothing else, see Thm C.2. in Appendix of this paper.) Then we will not be surprised to see that for example:
R01*(R04+1)*(W1+X1+Y1+Z1+R01+1)=0
which is the same as:
R01*(R04+1)*(W1+X1+Y1+Z1)=0
Now our new properties are yet stronger, we have only one affine factor:
(1+R16+R17+R20)*(W5+X5+Y5+Z5+1+R17) = 0
Moreover the connection between the size of annihilator space and the biases works both ways. We have also accidentally discovered that not only sums of 4 outputs but also things such as
(W5+X5+Y5+Z5+1+R17)
are strongly biased with the actual original DES S-boxes.
This is new, and was not observed before and not contained in properties presented by Shamir, or cannot be a consequence of these previously observed properties, as we added an affine function. It extends the properties discovered by Shamir with new correlations not studied before, and more importantly with linear annihilations and their applications in cryptanalysis. An actual attack which exploits this type of properties will be presented at ICISC 2019.
More generally we observe that a sum of all 4 outputs of some DES S-boxes can have more than one very strong correlation with linear functions. Is there are bigger picture we can see here? Yes, the set of all such correlations have been studied since 1970 [yes! in 1976 was already a routine tool, a proof can be found in slide 33 here] and today it is known under the name of Walsh spectrum. Here are the Walsh spectra for the sum of 4 outputs for the three DES S-boxes studied above:
W1+X1+Y1+Z1 {0: 19, 4: 27, 8: 11, 12: 3, 16: 1, 20: 1, 24: 1, 36: 1}
W4+X4+Y4+Z4 {0: 54, 16: 8, 32: 2}
W5+X5+Y5+Z5 {0: 32, 8: 30, 24: 1, 40: 1}
Extremely bad, yes? Well not quite.
We need to observe that this sort of things happen frequently even for Boolean functions chosen at random. It is clear that from the point of view of diffusion or the P-box, attacks which involve all the 4 outputs of each S-box are going to be the hardest to make, or will involve larger numbers of simultaneously active S-boxes. The fact that it happens here when all the 4 outputs are used and not with say W1+Y1, should possibly be considered as evidence that DES was designed to be particularly strong against our attacks. An attack able to exploit such properties exists however, and it was presented at ICISC 2019.
ADDED LATER:
Some versions of DES are substantially wekaer, other are stronger. For example S^5DES has a lot more 1-weak normal annihilations, eight times more than with DES. In contrast, in more recent versions of DES, with DESL and in S*DES, there are zero such events whatsoever.
A shameful provocation and sad day for scientific research: 11 years after the original publication Craig Wright has managed to re-publish Satoshi’s original paper with his name on it.

There is abundant literature on the security of Data Encryption Standard (DES or 3DES). Today we have released a new way to attack this cipher, see Section 11 in here. Anyone who reads this paper should immediately see that the high confidence which have developed over decades in research community about our ability to design secure block ciphers was never justified in any way and an incredibly rich space of attacks with unique powerful features is now available to study.

Added Jun. 2019: here are slides presented at CECC 2019 (invited talk).
Added Oct. 2019: here are slides presented at the 2019 Symposium on Cryptologic History, 17-19 October 2019, Kossiakoff Centre, Laurel, MD, USA. Here is the program.
Added December 2019: Here are the slides presented at ICISC conference in Seoul Korea, “Systematic Construction of Nonlinear Product Attacks on Block Ciphers”, on 4 December 2019.